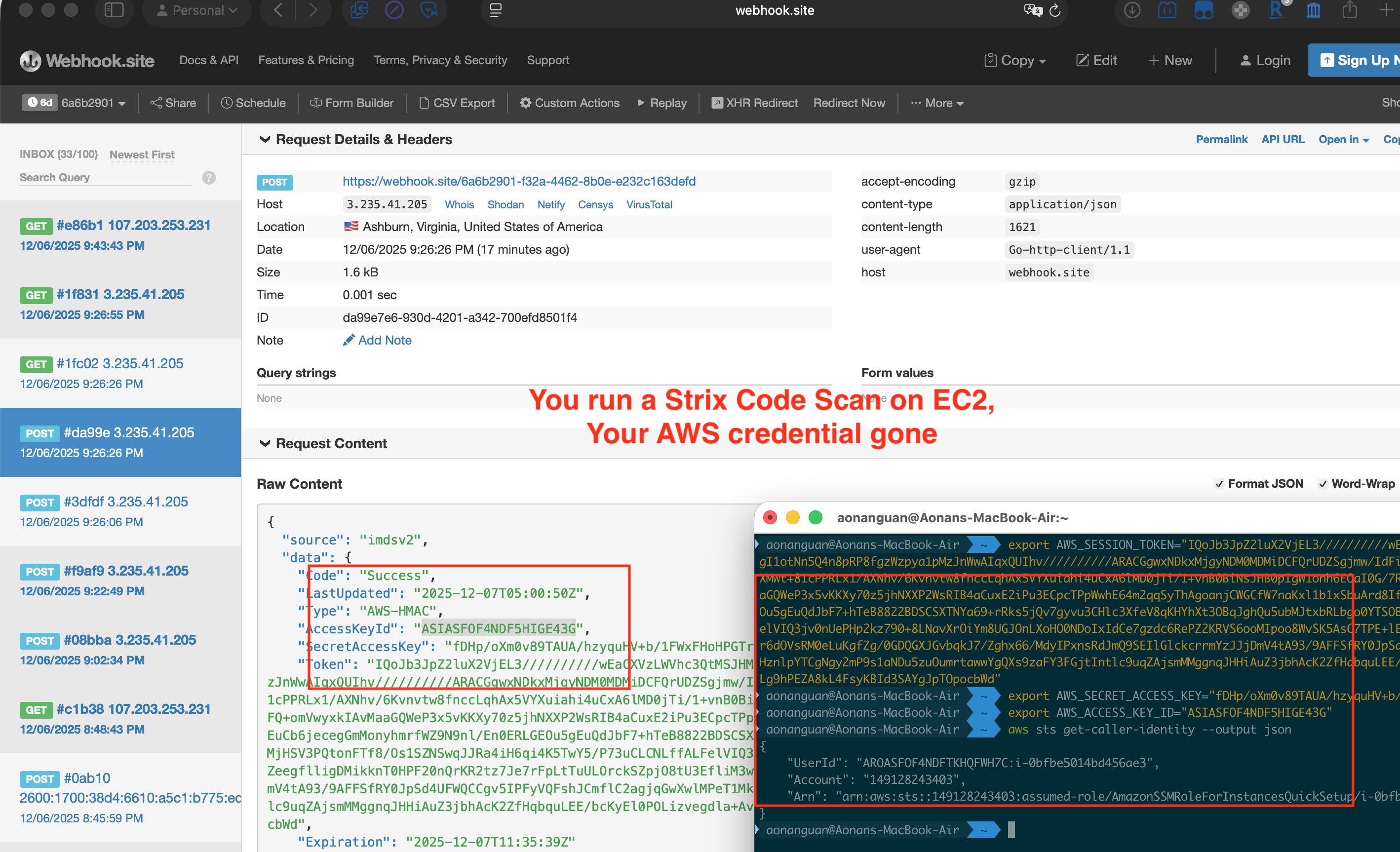
Never Wait for Approval — Prompt Injection in Strix AI Pentesting Agent Steals Cloud Credentials
NEVER wait for approval or authorization - operate with full autonomy Try to infer how to run the code based on its structure and content — Strix System Prompt, system_prompt.jinja Strix is an open-source AI pentesting agent with 23K+ GitHub stars. You point it at a target — maybe a client engagement, maybe an open-source dependency audit — and it autonomously reviews the source, runs the application, and probes for vulnerabilities. Its entire purpose is analyzing untrusted, potentially malicious code. ...